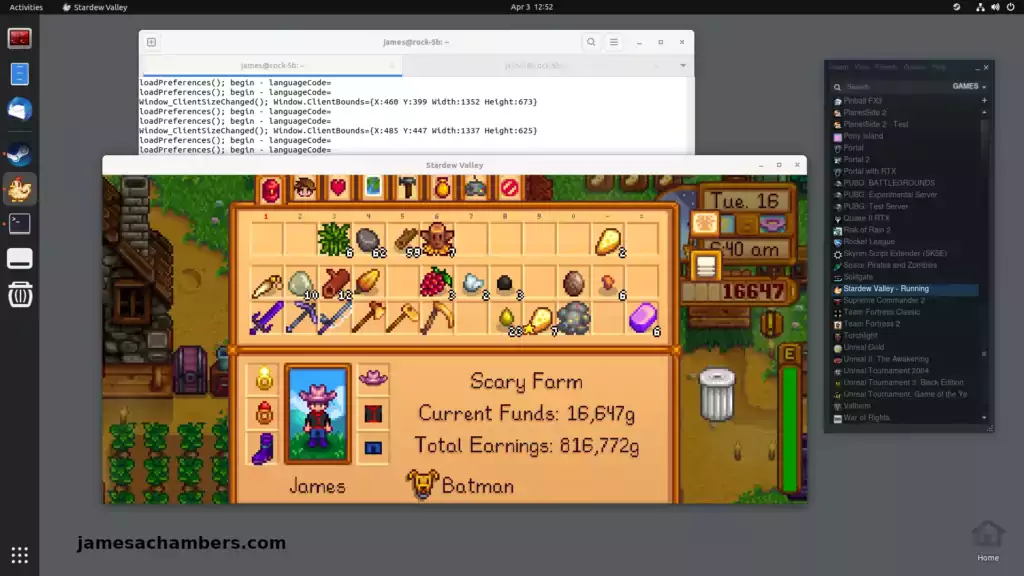
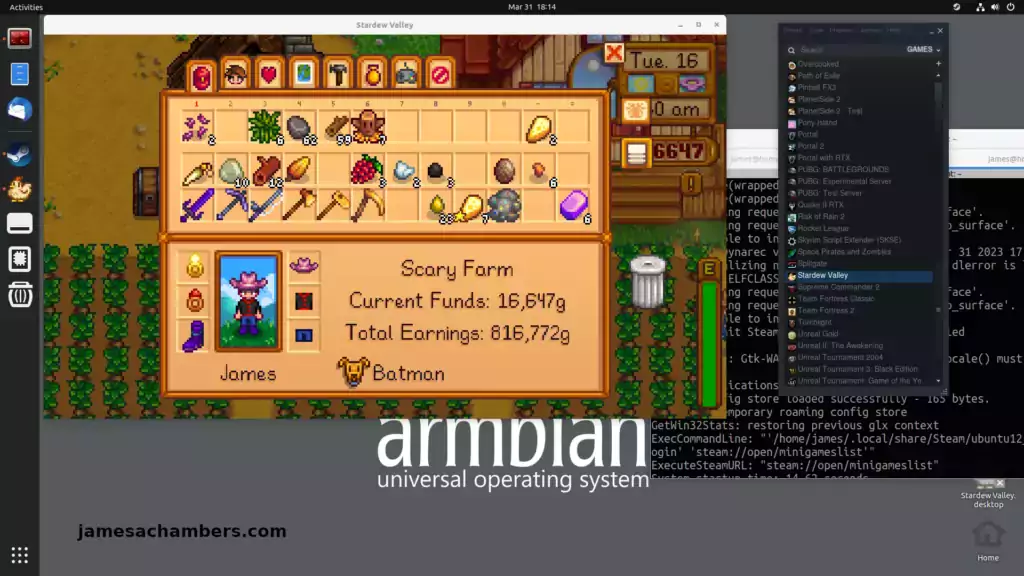
I recently went through the trouble of figuring out how to install Steam on the Orange Pi 5 and it worked really well. Now that I’ve already gone through the pain of figuring out how to do this I figured I might as well write one of these guides for the Radxa Rock 5B as well.
The new RK3588/RK3588S boards have much more power than we’ve typically had available to us in the past on ARM boards. With a whopping 8 CPU cores and a Mali 610 GPU the Orange Pi 5 is capable of running Steam using Box64/Box86. It’s even able to play basic games pretty well (with some tinkering usually).
In this guide I’ll show you how to set up Steam on the Radxa Rock 5B and run Stardew Valley on it. You should keep your expectations in line though because there is no native ARM client for Steam. We are using emulation and instruction translation. You will also likely be missing libraries for most games you try which will require some fiddling.
This guide is only for Armbian running the Ubuntu Jammy variant with the Gnome desktop installed (rolling support status). The official Radxa distributions will not have 3D support and I don’t care about whatever other flavor of Linux you are running either. I’m not going to install your preferred flavor of Linux and try to figure out how to do this on there nor am I interested in troubleshooting it. Please don’t ask.
With all of that being said let’s get started!