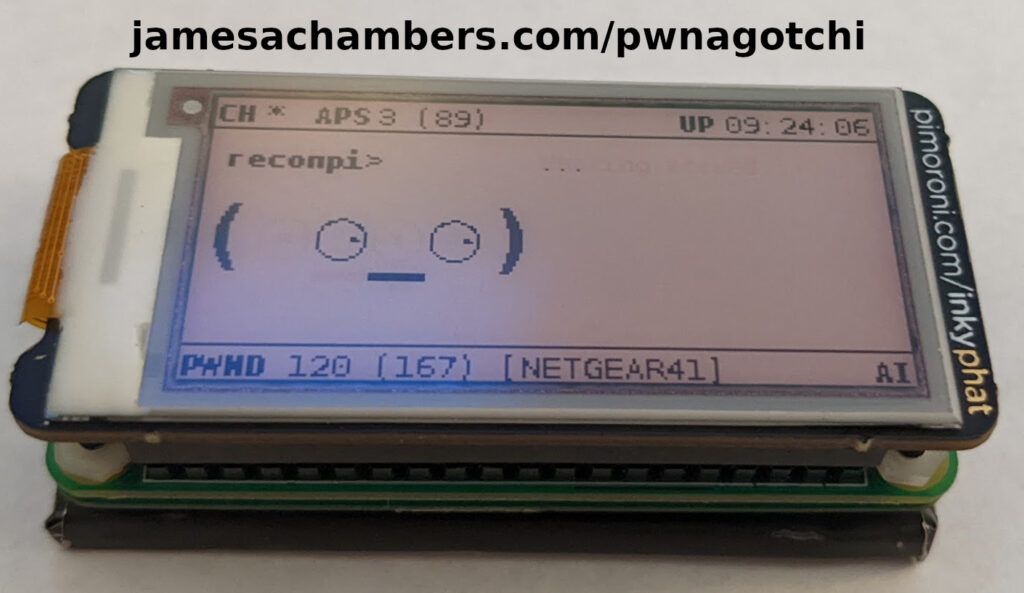
I’ve been mining cryptocurrency for a very long time. I’ve been recently building out my ASIC farm and I wanted to get an idea of how secure these are as I have a significant investment in this hardware. Considering that ASIC miners are machines that literally print money out of thin air (in the form of cryptocurrency) I figured they’d be quite secure. I haven’t seen any ASIC miner exploits found in years. That’s a good sign right?
Wrong. What happened was all of the ASIC manufacturers stopped releasing their source code. In the early days it was all available on GitHub. After the first set of hacks came out most of them close-sourced their firmware. But James, you might be saying, didn’t that work if there hasn’t been any exploits found this entire time?
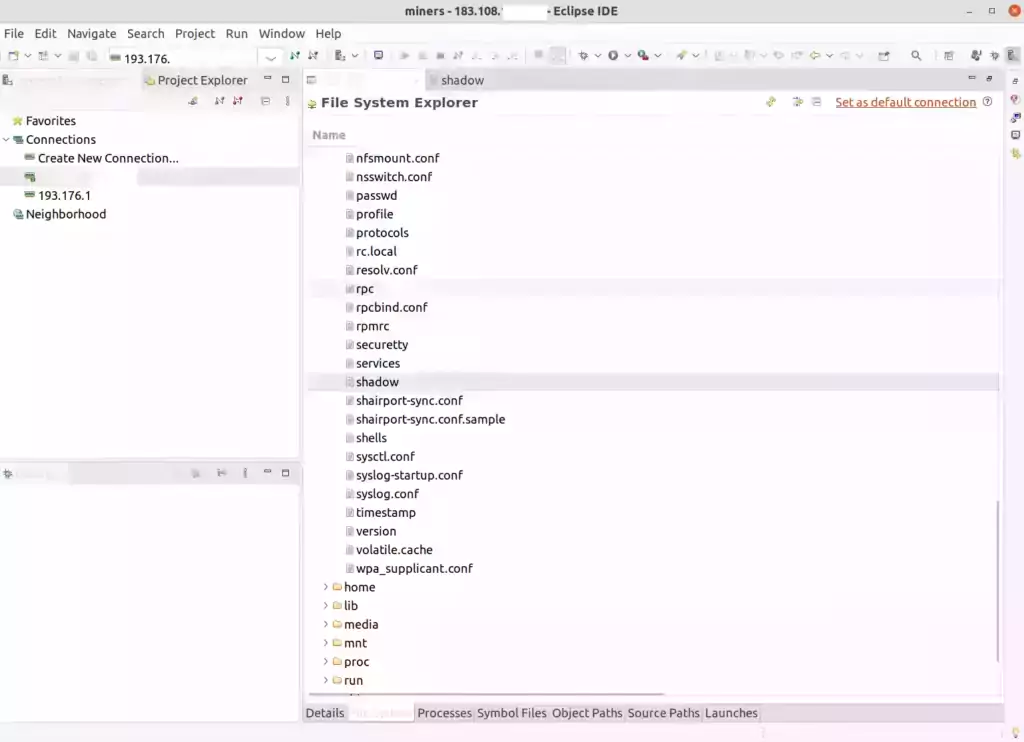
Negative. Security through obscurity only slows them down but in the end you are more vulnerable as so few eyeballs will ever see the source code. As a result the security is a joke and today I’ll be presenting extremely serious vulnerabilities for multiple ASIC mining manufacturers. They are definitely *not* secure. They are making mistakes that there’s no way would have happened if the firmware was open source as I will prove to you.
The point will be that you need to upgrade to the latest firmware to protect yourself and that you should *NEVER* port forward a port from the internet to your miner or you are going to get hacked for sure, and you always were. We’re going to discuss everything you need to protect yourself against these vulnerabilities and other future vulnerabilities that have yet to be discovered. Let’s begin!